FireBrick Bonding more than 3 lines
Overview
The FireBrick 2500/2700 has 4 ethernet ports, typically one port will be for the LAN connection (for example - to the main office switch), and the rest for connections to the ADSL/FTTC modems.
As there are 4 ports are we restricted to only bonding up to 3 ADSL/FTTC lines? No.
To overcome the physical port restriction a VLAN switch can be used - for example:
ADSL MODEM 1 -- ADSL MODEM 2 -- ADSL MODEM 3 -- VLAN Switch -- Firebrick -- LAN SWITCH == Computers ADSL MODEM 4 --
The switch would be set up for 4 (or more) separate VLANs on the appropriate ports, and on the FireBrick, the <ppp .../> config would have VLAN="n".
VLAN Switch Config
Here are some notes on setting up a HP ProCurve 1810G-8:
The HP ProCurve 1810G-8 (J9449A) is a nice little 8 port managed switch. No fans and similar in size to a FireBrick.
Overview
The FireBrick will have a single WAN port, which will plug in to the HP Switch. The ADSL/FTTC modems will plug in to the HP Switch too. This will then, with VLANs, enable the FireBrick to use up to 7 ADSL/FTTC modems.
- Default IP is "192.168.2.10"
- Default Password is blank
Save Config
To make things a little easier, here is a saved config: File:FBVLANconfig1810G.bin.zip. It is the default config (default IP and password), but with VLANs as follows:
- Port 1 - VLAN 101, for ADSL line 1
- Port 2 - VLAN 102, for ADSL line 2
- Port 3 - VLAN 103, for ADSL line 3
- Port 4 - VLAN 104, for ADSL line 4
- Port 8 is for the FireBrick
The config was from HP ProCurve 1810G - 8 GE, P.1.17, eCos-2.0, Software Version, P.1.17
However it only takes a few minutes to set up the VLANs manually as follows:
Basic Settings
- Set your computer to an IP in the same subnet as the switch, e.g. 192.168.2.11
- Plug computer in to a port, e.g. port 7
- Log in to http://192.168.2.10 with a blank password
- Maybe set the system description details
- Set admin password (Maintenance - Password Manager) then save and re-login
- Enable HTTPS (Security - Secure Connection) generate certificate and apply
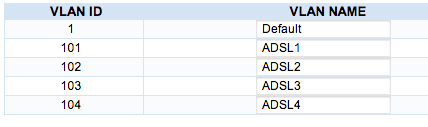
Create VLANs
We will set ports 1-4 to be VLANs 101, 102, 103, 104. We'll use port 8 for plugging in to the FireBrick, and use port 7 for our admin.
- Create 4 VLANs (VLANS - VLAN Configuration)
- Set the names to be ADSL1, ADSL2, ADSL3, ADSL4 - this will match the login/line numbers of the ADSL/FTTC lines
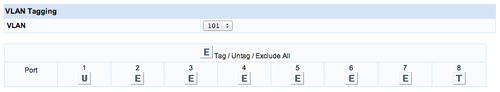
Configure ports for VLAN tagging
- Under VLANs - Participation Tagging:
- set VLAN 101 to be U on port 1 and T on port 8. E on rest
- set VLAN 102 to be U on port 2 and T on port 8. E on rest
- set VLAN 103 to be U on port 3 and T on port 8. E on rest
- set VLAN 104 to be U on port 4 and T on port 8. E on rest
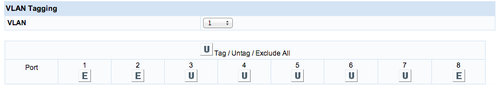
- set VLAN 1 to be E on port 1, 2, 3, 4 and U on port 5, 6, 7, 8
- SAVE CONFIG - otherwise you will learn the hard way
IP Address
In order to access the Switch, we'll need to setup an interface on the FireBrick with a subnet in the same range as the switch. We can use the default 192.168.2.0/24, and this will be accessible from the LAN side. Alternately, we can use a public /30. This will involve a new /30 allocation on Clueless, routed to all the ADSL/FTTC lines, and on the FireBrick a subnet on the WAN interface. Set the gateway to the FireBrick, then the switch can access things like time server, syslog server etc...