FireBrick Road Warrior OSX: Difference between revisions
mNo edit summary |
mNo edit summary |
||
| Line 2: | Line 2: | ||
It is possible to connect an Apple Mac with OSX to a FireBrick over IPSEC with IKEv2 and EAP. Regrettably the IPSEC facilities within OSX before version 'El Capitan' are not fully enough featured to achieve this alone, so some additional VPN client software can be installed called StrongSwan. |
It is possible to connect an Apple Mac with OSX to a FireBrick over IPSEC with IKEv2 and EAP. Regrettably the IPSEC facilities within OSX before version 'El Capitan' are not fully enough featured to achieve this alone, so some additional VPN client software can be installed called StrongSwan. Details below describe how to install the CA certificate from the FireBrick to your Apple computer and then how to set up the VPN connection either by using El Capitan's built in VPN settings or by using StronSwan. |
||
| ⚫ | |||
| ⚫ | |||
| ⚫ | Visit [http://download.strongswan.org/osx/ the download site] and download the latest binary. At the time of writing the latest version was '''strongswan-5.3.2-1.app.zip'''. Allow the machine to unarchive it; usually by selecting the "Open with Archive Utility" option. This will deposit the StrongSwan.app into your downloads directory. Drag the app from the downloads directory into your Applications folder. This completes installation of the StrongSwan Client. |
||
| ⚫ | |||
| ⚫ | |||
| ⚫ | |||
== Getting the CA from the FireBrick == |
== Getting the CA from the FireBrick == |
||
| Line 37: | Line 27: | ||
</gallery> |
</gallery> |
||
=OSX versions 10.11, 'El Capitan' and above= |
|||
| ⚫ | |||
==Create the Connection== |
|||
#Go to Apple Menu - System Preferences |
|||
#Go to Network |
|||
#Click the + Icon on the bottom/left, and choose: |
|||
#*Interface: VPN |
|||
#*VPN Type: IKEv2 |
|||
#*Service Name: eg 'FireBrick' or 'Office' |
|||
#On the next window fill in the information. |
|||
=OSX version 10.10,'Yosemite' and below= |
|||
For versions before 10.11 you'll need to use the StronSwan program: |
|||
| ⚫ | |||
| ⚫ | Visit [http://download.strongswan.org/osx/ the download site] and download the latest binary. At the time of writing the latest version was '''strongswan-5.3.2-1.app.zip'''. Allow the machine to unarchive it; usually by selecting the "Open with Archive Utility" option. This will deposit the StrongSwan.app into your downloads directory. Drag the app from the downloads directory into your Applications folder. This completes installation of the StrongSwan Client. |
||
| ⚫ | |||
| ⚫ | |||
| ⚫ | |||
==Configure strongSwan== |
==Configure strongSwan== |
||
Run strong swan by either: |
Run strong swan by either: |
||
Revision as of 19:18, 28 October 2015
It is possible to connect an Apple Mac with OSX to a FireBrick over IPSEC with IKEv2 and EAP. Regrettably the IPSEC facilities within OSX before version 'El Capitan' are not fully enough featured to achieve this alone, so some additional VPN client software can be installed called StrongSwan. Details below describe how to install the CA certificate from the FireBrick to your Apple computer and then how to set up the VPN connection either by using El Capitan's built in VPN settings or by using StronSwan.
Getting the CA from the FireBrick
Note: this guide doesn't go into actual configuration of the FireBrick to be an endpoint, merely how to connect your Mac client to it. Therefore it is assumed the certificate already exists on the FireBrick. It may also be that this is emailed to you by whoever maintains your FireBrick, in which case skip this step.
- Log into the Firebrick.
- Click on the Config menu in the bar on the left.
- Click on the Certificates menu beneath that.
- You should be presented with a list of certificates installed. Each line will look approximately as follows :
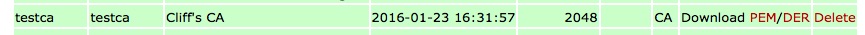
- At the right hand end of the row corresponding the the certificate you wish to download, click on the PEM link.
Installing the CA certificate into OSX
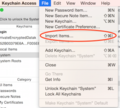
- Go to: Applications - Utilities - Keychain Access
- In the top/left area named 'Keychains, click on System
- In the bottom/left are named 'Category', click on Certificates
- Go to: File - Import Items
- Select the file you've downloaded, eg ca-cert.pem
- Review the certificate and then select Always Trust, you may be asked to confirm your apple user password.
OSX versions 10.11, 'El Capitan' and above
If you have 'El Capitan' then the built in VPN connection settings should just word. You will still need to install the Certificate as above, but you can skip the StrongSwan parts below and just use the Network Settings to add a VPN IKEv2 connection.
Create the Connection
- Go to Apple Menu - System Preferences
- Go to Network
- Click the + Icon on the bottom/left, and choose:
- Interface: VPN
- VPN Type: IKEv2
- Service Name: eg 'FireBrick' or 'Office'
- On the next window fill in the information.
OSX version 10.10,'Yosemite' and below
For versions before 10.11 you'll need to use the StronSwan program:
Downloading & installing the StrongSwan Native Client
Visit the download site and download the latest binary. At the time of writing the latest version was strongswan-5.3.2-1.app.zip. Allow the machine to unarchive it; usually by selecting the "Open with Archive Utility" option. This will deposit the StrongSwan.app into your downloads directory. Drag the app from the downloads directory into your Applications folder. This completes installation of the StrongSwan Client.
Configure strongSwan
Run strong swan by either:
- Go to Applications and click on the strongSwan icon
- Use the 'spotlight' search tool neat the clock to search for strongSwan
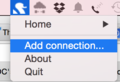
You'll then have a swan icon in your clock tool bar at the top (it actually looks like a Dalek!) (Screenshot below)
- Click Add Connection (Screenshot below)
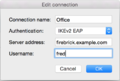
- Name: eg FireBrick (Screenshot below)
- Authentication IKEv2 EAP
- Server address: IP or Name of your FireBrick
- Click OK
Connect!
- Click on the
DalekStrongSwan icon once more, - Click your connection name then connect.
- The first time, you may be asked to install a 'Helper' application for Strong Swan, your computer password will be required
- You'll be prompted for the password, this is the one as set up in the EAP Identity on the FireBrick (in this example, we had set up a user of fred with a password)
Error: Unsupported integrity algorithm
There is one "gotcha" with StrongSwan on MAC though - it may negotiate an encryption algorithm for the data connection which OS X doesn't support, the FireBrick will create a log like:
failed to create ESP context: unsupported integrity algorithm AES_XCBC_96
This really a bug in the way the StrongSwan app was built - it shouldn't negotiate AES if the underlying OS can't do it (which as of July 2015 OSX can't manage AES). However, the easy workaround is to set up an ipsec-proposal to avoid this:
- On the FB config editor create a 'Proposals for IPsec AH/ESP security association'.
- Give is a name, and set, for example, HMAC-SHA1 for authset.
- Then, back in the 'IPsec IKE connection settings' select the new Proposal in the 'ipsec-proposals' drop down.
Here is example config for this:
<IPsec-proposal name="custom" authset="HMAC-SHA1"/>