Stopping Open DNS - Billion: Difference between revisions
(Created page with "=Billion= Billion routers appear to have a built-in DNS resolver, and answer queries on the WAN interface by default, so is vulnerable to taking part in DDoS attacks by reply...") |
No edit summary |
||
| Line 8: | Line 8: | ||
Please note that on these routers this does not prevent the router's internal resolver from doing the DNS lookup itself. This isn't usually a problem, but due to recent DNS amplification attacks sometimes lookups have continued after fixing the original problem. To prevent this add a rule blocking DNS *from* the router's WAN IP *to* port 53. This will prevent usage of the router as the LAN's DNS resolver. |
Please note that on these routers this does not prevent the router's internal resolver from doing the DNS lookup itself. This isn't usually a problem, but due to recent DNS amplification attacks sometimes lookups have continued after fixing the original problem. To prevent this add a rule blocking DNS *from* the router's WAN IP *to* port 53. This will prevent usage of the router as the LAN's DNS resolver. |
||
[[:Category:Open DNS Resolvers]] |
|||
Revision as of 10:04, 18 June 2013
Billion
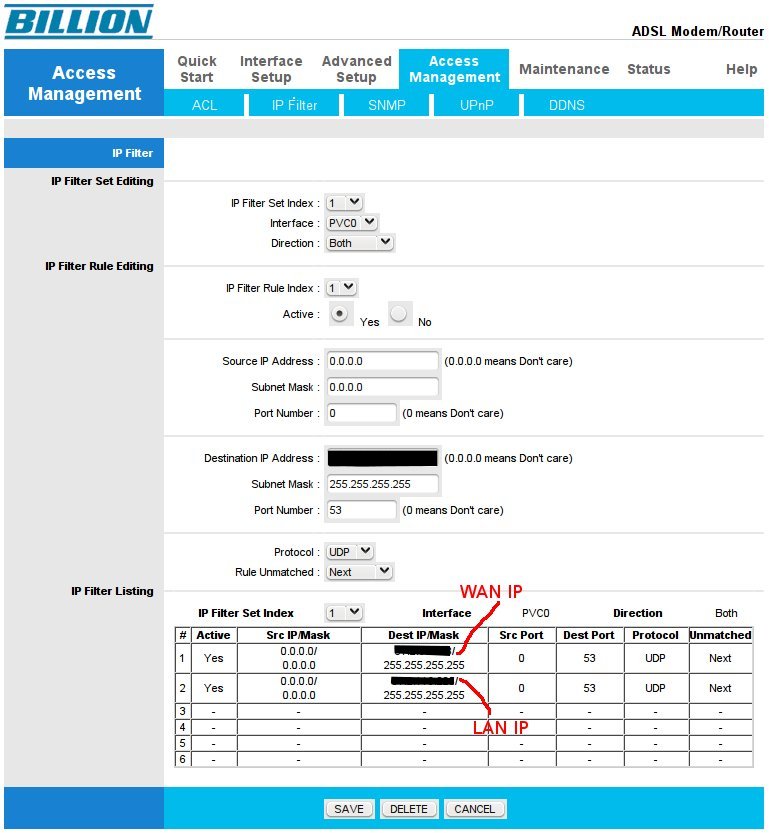
Billion routers appear to have a built-in DNS resolver, and answer queries on the WAN interface by default, so is vulnerable to taking part in DDoS attacks by replying to spoofed dns queries. Screenshot below shows how to block this in filters.
This was tested on Firmware Version : 2.7.0.23(UE0.C2C)3.5.10.1
Please note that on these routers this does not prevent the router's internal resolver from doing the DNS lookup itself. This isn't usually a problem, but due to recent DNS amplification attacks sometimes lookups have continued after fixing the original problem. To prevent this add a rule blocking DNS *from* the router's WAN IP *to* port 53. This will prevent usage of the router as the LAN's DNS resolver.